
REQUEST A DEMO
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.

AI-enabled attacks and digital fraud operations are moving faster than most security programs can adapt. Threat actors are blending traditional intrusion techniques with adversarial machine learning, prompt manipulation, bot automation, and payment fraud tactics often within the same campaign.
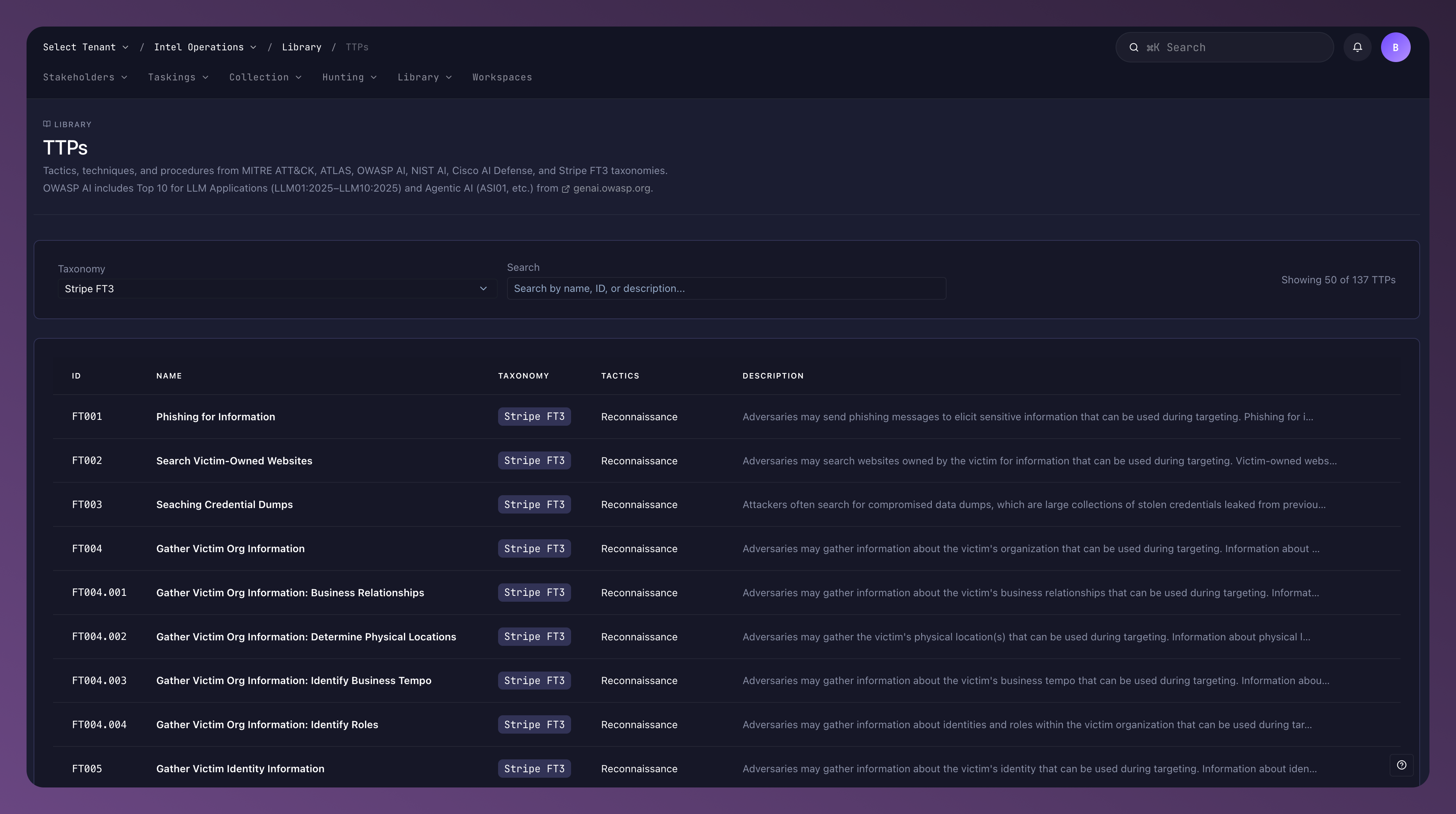
To help organizations respond to this shift, Threatnote now integrates the following taxonomies directly into the platform as structured TTP objects:
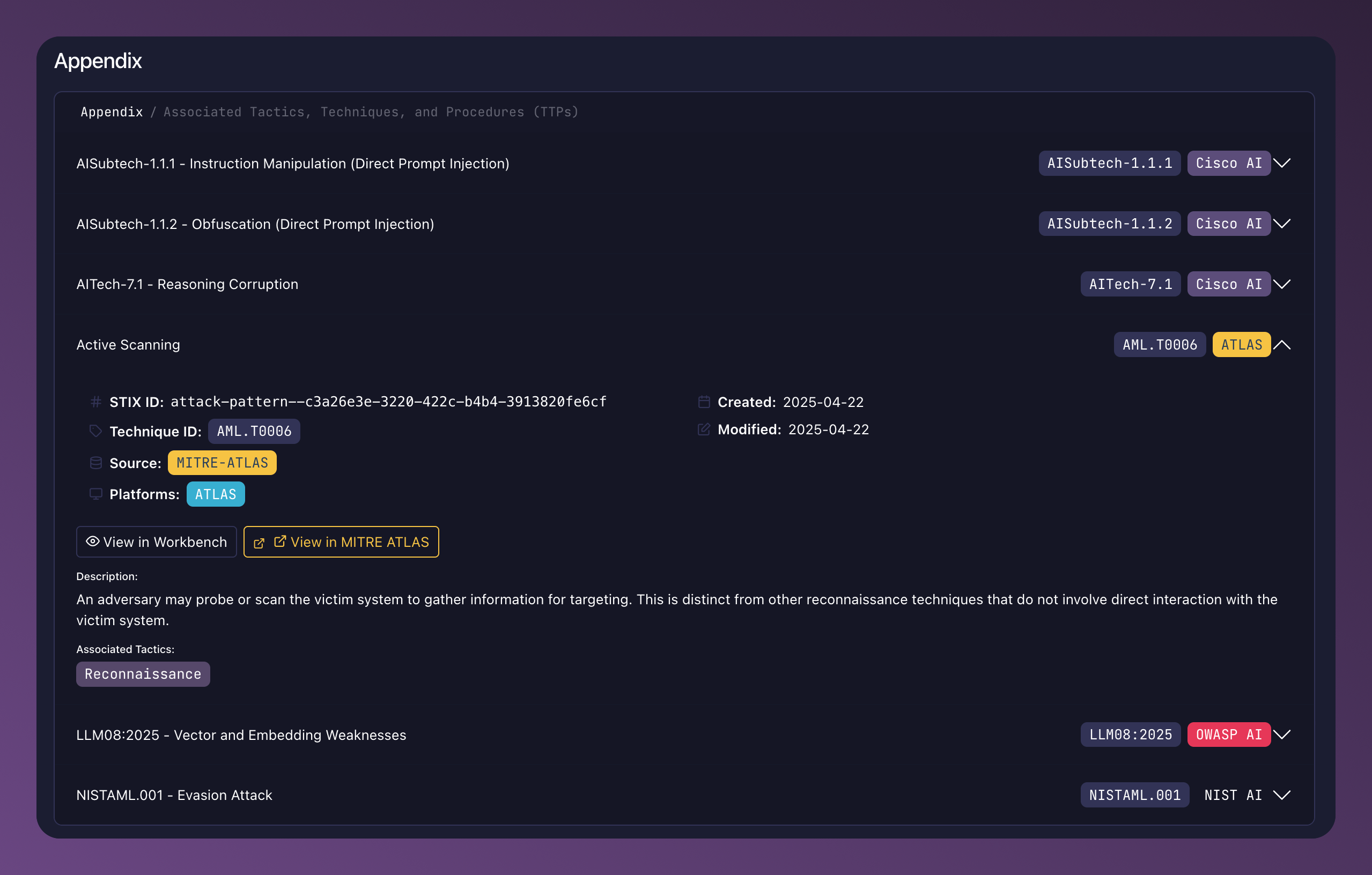
These taxonomies are not simply referenced in documentation. They are operationalized inside Threatnote as STIX-native TTP objects, enabling structured alignment across detection engineering, threat hunting, fraud intelligence, and reporting.
This is a meaningful expansion of our commitment to delivering intelligence that works together.
Security and fraud teams are no longer operating in isolated domains.
Historically, these behaviors have been tracked in separate frameworks and separate tools. ATT&CK covered enterprise techniques. ATLAS addressed adversarial ML. OWASP outlined AI application risks. Stripe’s FT3 taxonomy formalized fraud operations.
What has been missing is a way to unify them operationally.
Threatnote now bridges these frameworks through structured STIX modeling and cross-taxonomy alignment.
All integrated taxonomies are represented in Threatnote as STIX objects:
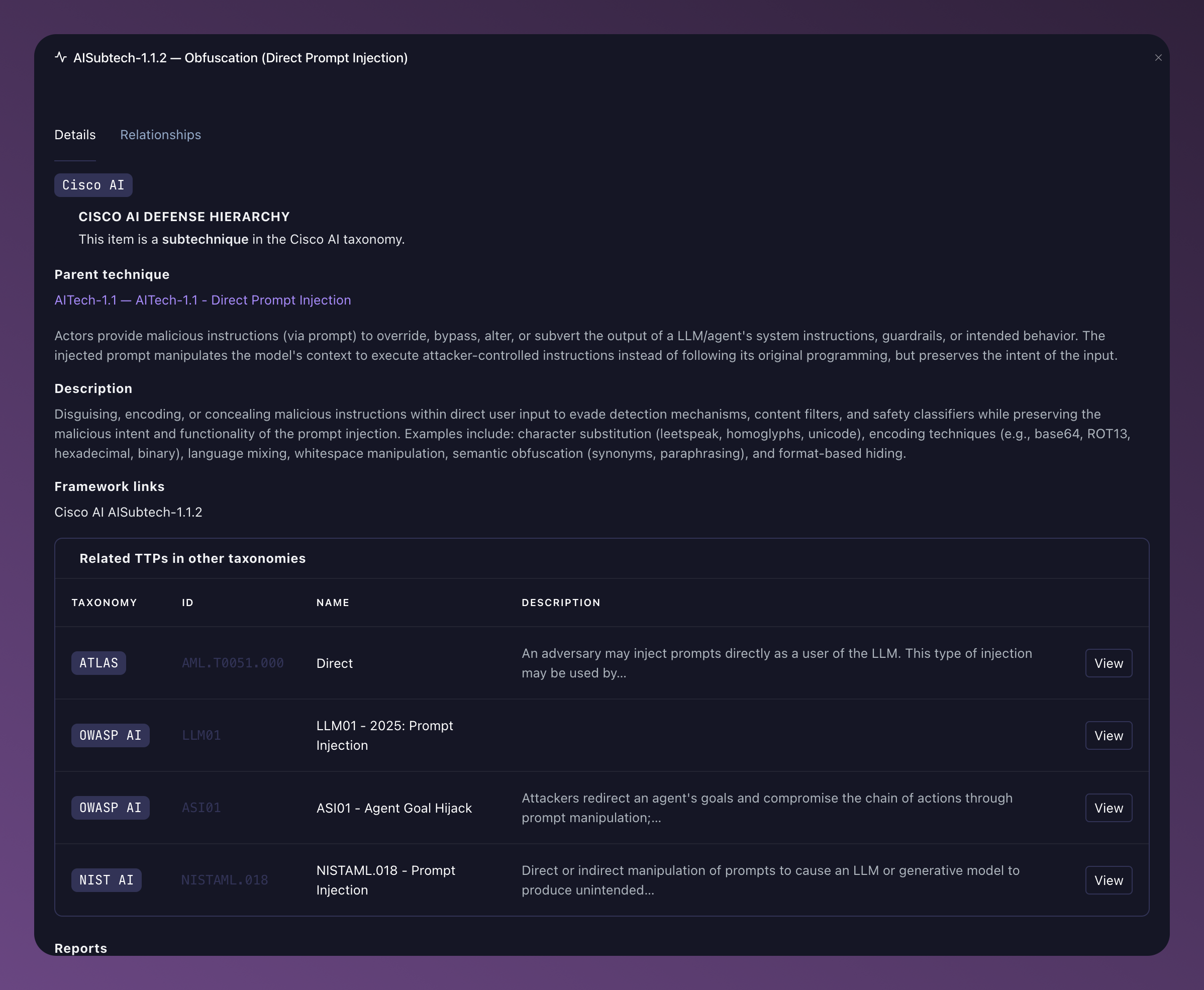
Each TTP from ATT&CK, ATLAS, OWASP AI, NIST AI, Cisco AI Defense, and Stripe FT3 is modeled as a first-class object in the platform.
More importantly, they are aligned to one another using STIX relationships such as:
For example:
Because these are structured STIX relationships, analysts can pivot across taxonomies instantly. A technique observed in fraud telemetry can be traced to related infrastructure tactics, AI manipulation patterns, and known intrusion sets.

This alignment transforms frameworks from static references into a connected intelligence graph.
Customers gain a single view of:
Instead of siloed taxonomies, everything is normalized into one intelligence model.
Detection signatures inside Threatnote can now be mapped directly to:
Because these mappings are represented as STIX relationships, coverage can be measured across multiple frameworks simultaneously.
Customers can:
This provides measurable maturity progression rather than anecdotal reporting.
Threat hunts can now target:
Hunt findings can be linked to TTP objects through STIX relationships, allowing organizations to track recurring technique usage over time.
As more telemetry is ingested from sources like dark web monitoring, digital risk protection modules, vulnerability intelligence, and external STIX/TAXII feeds, related intelligence is automatically enriched and connected to provide broader context.
Threat actors increasingly operate across boundaries.
An intrusion set may:
Within Threatnote, intrusion sets are linked to all associated TTP objects through uses relationships.
Because ATLAS, OWASP AI, NIST AI, Cisco AI Defense, and Stripe FT3 techniques are represented as compatible STIX objects, actor profiling now spans AI abuse and fraud behaviors alongside traditional intrusion activity.
This provides a more complete behavioral fingerprint of adversaries.
Threatnote consolidates TTP data from:
Each piece of intelligence is normalized into STIX objects and relationships.
As a result:
This is the practical realization of intelligence that works together, with structured data flowing into a shared object model where techniques, actors, detections, and reports are all interconnected.
Organizations deploying AI systems must manage:
By embedding leading AI and fraud taxonomies into the Threatnote intelligence fabric, customers can:
All of this occurs within a unified STIX-based graph that supports pivoting, visualization, enrichment, and export.
The integration of ATT&CK, ATLAS, OWASP AI, NIST AI, Cisco AI Defense, and Stripe FT3 is part of a broader initiative to expand structured technique coverage across emerging domains.
As adversaries adopt AI tooling and fraud ecosystems mature, Threatnote will continue:
Security programs are increasingly measured by how well they can correlate signals across domains.
By unifying AI, fraud, and traditional intrusion taxonomies within a STIX-native intelligence model, Threatnote provides customers with a structured way to operationalize that correlation.
All integrated taxonomies and newly incorporated TTPs are available within the Library section of Threatnote, under a dedicated TTP area where users can explore detailed descriptions, cross-taxonomy mappings, and framework-specific context for each technique.
That is what it means to build intelligence that works together.